Private IP endpoints are the backbone of many secure digital environments, enabling organizations to run powerful tools without exposing them publicly. One such endpoint is 172.16.252.214:4300, which represents a private network address combined with a specific port used to host an internal service. Understanding how such endpoints function helps developers, system administrators, and businesses manage their infrastructure more effectively.
Breaking Down the Structure of the Address
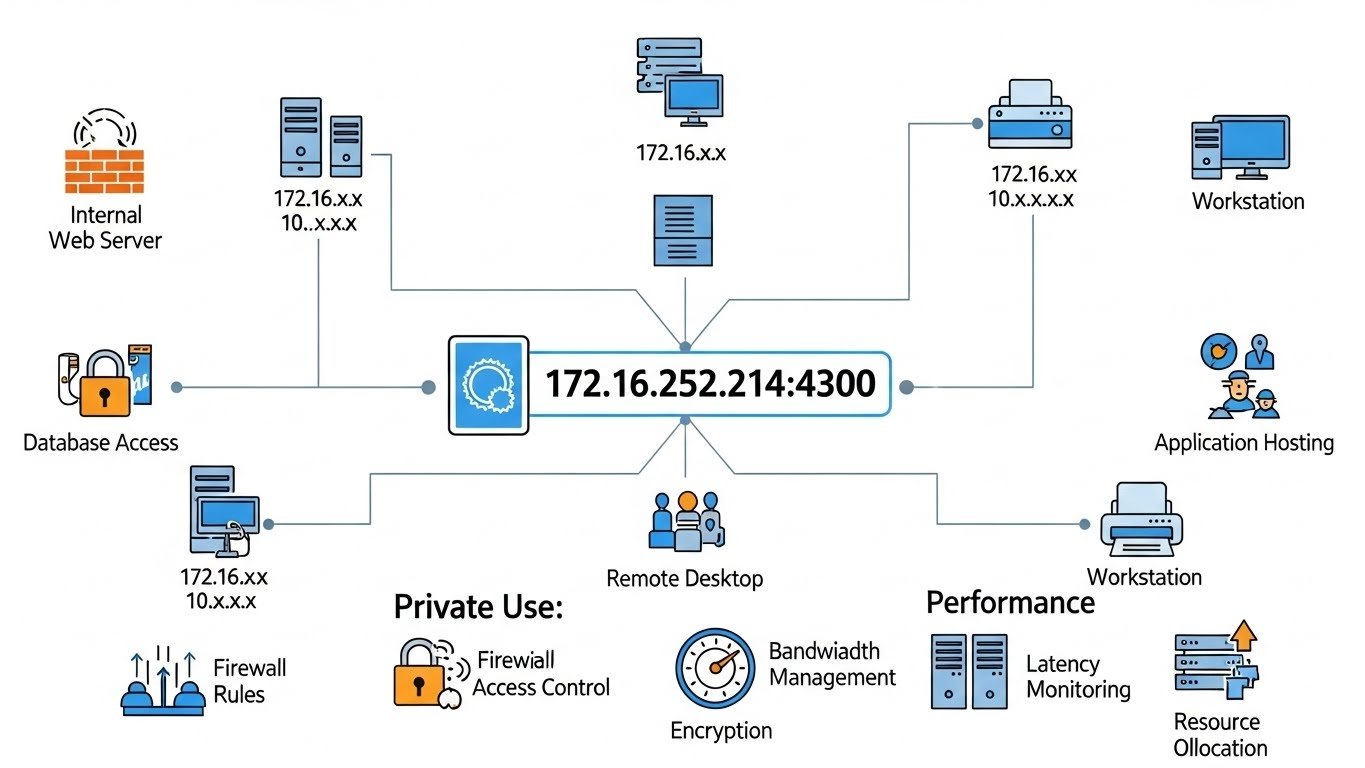
The IP portion of 172.16.252.214:4300 falls within a private range reserved exclusively for internal networks. These addresses are intentionally excluded from public internet routing. The port number, 4300, specifies the exact service running on the host machine. Together, they create a precise destination that allows users and systems to communicate with the correct application without ambiguity.
Why Organizations Rely on Internal Endpoints
Companies prefer endpoints like 172.16.252.214:4300 because they offer control and predictability. Internal dashboards, staging servers, and automation tools often operate on private ports to reduce exposure. This setup allows teams to test features, monitor systems, and manage configurations without worrying about public traffic or external threats interfering with daily operations.
Development and Testing Environments
In development workflows, 172.16.252.214:4300 may be used to host a local or shared testing application. Developers can deploy changes, review logs, and debug issues in real time. Using a fixed internal endpoint ensures consistency across teams, making collaboration smoother. It also keeps unfinished or experimental features safely isolated from live production environments.
Administrative and Monitoring Tools
System administrators often assign endpoints like 172.16.252.214:4300 to internal admin panels or monitoring solutions. These tools track server health, resource usage, and application performance. Since access to 172.16.252.214:4300 is restricted to the internal network, sensitive operational data remains protected while still being readily available to authorized staff.
Security Layers That Strengthen Private Services
Although 172.16.252.214:4300 is not publicly accessible, security should never be an afterthought. Strong authentication mechanisms, permission controls, and encrypted communication add critical layers of protection. Many organizations also audit activity on 172.16.252.214:4300 to ensure compliance and quickly detect irregular behavior. Internal security is just as important as external defense.
Network Configuration and Optimization
Proper configuration ensures that 172.16.252.214:4300 runs efficiently. Administrators may adjust firewall rules, routing policies, or bandwidth limits to optimize performance. Because traffic is confined to the internal network, response times are usually fast. Fine-tuning these settings helps maintain stability even as the number of users or connected services grows.
Common Issues and How to Resolve Them
If users cannot reach 172.16.252.214:4300, the problem often lies in network access, service availability, or port conflicts. Verifying that the application is running and listening on the correct port is a good starting point. Clear documentation about the purpose and configuration of 172.16.252.214:4300 makes troubleshooting faster and reduces downtime during critical moments.
Scaling and Future-Proofing
As organizations expand, services hosted on 172.16.252.214:4300 may need to scale. Containerization, virtualization, or internal load balancing can distribute demand while preserving the same access pattern. Planning ahead ensures that the endpoint remains reliable and adaptable, even as infrastructure requirements change.
Conclusion
Endpoints like 172.16.252.214:4300 quietly support many essential operations within private networks. They provide a secure, efficient way to host internal services, from development tools to administrative dashboards. By combining thoughtful configuration, strong security practices, and proactive management, organizations can ensure that 172.16.252.214:4300 continues to deliver value as systems evolve.